
Digital systems are used in organizations in all industries to process operations, hold sensitive information, and aid in communication. With the growth in the digital uptake, information security has become an essential business concern. A lot of workers take on a Cyber Security Course in Chennai as a way of understanding the way organizations can protect systems against the current threats. A good cybersecurity plan helps organizations diminish the risks, secure data, and stabilize long-term operations.
Understanding the Importance of a Cyber Security Strategy
A cybersecurity strategy is a systematic course that lays out the manner in which an organization ensures the security of its systems, networks, and information. It makes sure that the security practices are in line with business goals as opposed to operating separately. Lack of a clearly defined strategy exposes organizations to increased vulnerability to cyber threats that may affect services and reputation.
The overall strategy can assist organizations in putting security into daily operations. This compatibility enables companies to react well to threats without compromising productivity and growth.
Assessing Risks and Identifying Critical Assets
Evaluating Organizational Risks
Risk examination is the first step in building an excellent cybersecurity strategy. Companies need to test their infrastructure, applications, and data flows and determine weak points. Knowledge of the risks likely to occur makes leadership teams focus on security and distribute resources effectively.
Identifying High Value Information
Various categories of data need various degrees of protection. The most important information must be provided with the highest degree of security, including financial records, customer information, and proprietary data. The identification of important assets makes the protection strategies target the areas with the most impact.
Establishing Clear Security Policies and Governance
Defining Roles and Responsibilities
An effective governance framework enhances cybersecurity interventions. The employees should be aware of their roles in the system and data protection. Specific positions eliminate confusion and accountability in various departments.
Creating Strong Security Policies
The use of policies on security determines how acceptable the system may be used, access to data, and how to handle information. Policies that are well documented minimize the chances of unintentional violations and give the organization a stable decision-making framework. These policies also contain regulatory and legal compliance requirements.
Promoting Employee Awareness and Training
Building Cyber Security Awareness
The behavior of human beings is of great importance to the security outcomes. The employees are to be trained to identify threats, including phishing attacks and suspicious activity. The awareness programs minimize the risks that are caused by humans and enhance the overall security position. In order to develop the practical skills of vulnerability identification and attacker methods further, many of them become Ethical Hacking Course in Chennai and can become a useful contributor to the organizational security.
Encouraging a Security Conscious Culture
An effective cybersecurity policy also creates a culture of employees that treasures security programs and embraces them. Security awareness is incorporated in the day-to-day operations, and it will provide organizations with proactive risk prevention and expedited incident reporting.
Implementing Effective Technical Controls
Securing Networks and Systems
A cybersecurity strategy is based on technical safeguards. Access controls, firewalls, and system monitoring tools are used to prevent unauthorized access. Updates and regular maintenance also minimise vulnerabilities that may be used by attackers.
Protecting Data Through Secure Practices
The controlled access and secure storage of data are some of the data protection measures that ensure confidentiality and integrity. It is highly important that sensitive information is protected at all stages of its life to enhance the resistance of the organization to a breach.
Monitoring Systems and Managing Incidents
Continuous Security Monitoring
Continuous observation assists organizations in identifying abnormal conduct and any threat before it happens. Real-time visibility enables the teams to be prompt in their actions and avoid small hitches from worsening into major incidents.
Incident Response Planning
An incident response plan is a plan for how security breaches should be handled. Specific procedures lessen misunderstanding in incidents and help organizations recover more quickly. Frequent drills will mean preparedness and assurance of response. DevOps Training in Chennai enables professionals to acquire practical knowledge that allows them to incorporate automated monitoring and fast response practices that improve the effectiveness and reliability of incident management.
Ensuring Compliance and Continuous Improvement
Meeting Regulatory Expectations
Adherence to data protection policies is a necessity in most organizations. An organized cybersecurity plan will help to ensure compliance with legal parameters and industry standards and enhance the confidence of the stakeholders.
Adapting to Evolving Threats
The world of cyber threats keeps changing and updating its strategies. Frequent reviews and enhancements enable organizations to be ahead of the emerging risks and technology changes.
Aligning Security With Business Objectives
Cybersecurity must be used to support business expansion and not to cripple innovation, and organizations should be able to use new technologies, but they must manage the risks in a responsible manner. By confirming that security planning is in line with the organizational objectives, the businesses are able to remain agile without jeopardizing security. An effective cybersecurity plan would unite risk evaluation, governance, technical controls, staff awareness, and constant tracking to establish a robust defensive framework. The proactive and structured approach of organizations can better equip them to protect digital assets and react to changing threats. When professionals acquire useful cybersecurity skills by training at FITA Academy, they are equipped with the knowledge needed to align security programs with business goals, achieve stability and long-term reliability, and ensure business success.
Powered by Froala Editor
You may also like
More from this category.

3 Slides for Men That Keep Travel Effortless and Comfortable

Why Professional CDL Training Matters More Than Ever

8 Casino Games That Keep Players Coming Back to Khelo24Bet Casino

How to Start Using Winmatch360 in a matter of minutes
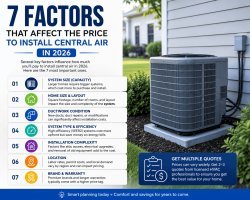
7 Factors That Affect the Price to Install Central Air in 2026

How Much Does It Cost to Install Central Air in 2026?

Cơ Sở Dữ Liệu Xuất Khẩu Cà Phê Việt Nam 2025: Phân Tích Các Nhà Xuất Khẩu Cà Phê Hàng Đầu Việt Nam và Xuất Khẩu Việt Nam Theo Quốc Gia

QuickBooks Desktop for Mac 2026: Comprehensive Download Guide

Essentials Hoodie France | Hoodies, Sweatshirts et Vêtements Streetwear Premium

